Going
Beyond
Passwords
Vidit Desai, Client Systems Architect
Vidit Desai, Client Systems Architect
In recent years, many firms have updated their password policies. But those policies may already be outdated, as security best practices for password complexity and expiry have been largely superseded by adoption of MFA (multi-factor authentication). If you’ve implemented MFA, you can safely adjust password policies to ease the burden on your users. For example, if you require a 25-character complex password (including special characters) and have MFA deployed, there’s no need to <expire passwords every few months; a hacker would need many lifetimes to crack the password and be unable to authenticate as a user without MFA. Since internal accounts typically do not have MFA, long and complex passwords should still be required for critical service accounts and similarly sensitive internal admin / ”god” accounts. However, for external accounts, using dual-factor options without passwords will result in stronger security than mandating extremely complex passwords.
To ease the everyday burden on users I recommend implementing new options for passwordless authentication. Passwordless authentication simply means MFA without a password: authenticating with other methods other than a password, such as biometrics, one-off email, or phone verification. MFA is often thought of as a second factor -in addition to a password- typically tied to a phone and approved with a phone call, push, or temporary numerical code. But MFA is more than that. “Multi-factor” implies high-level security “factors”:
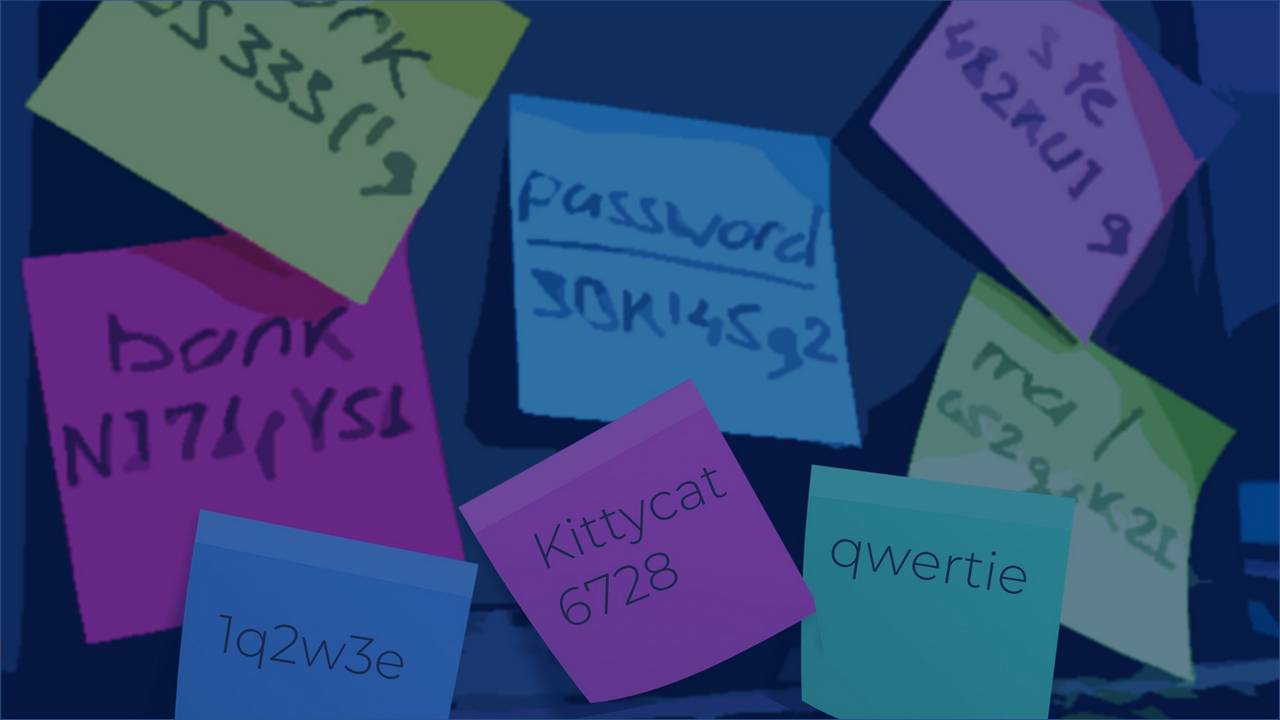
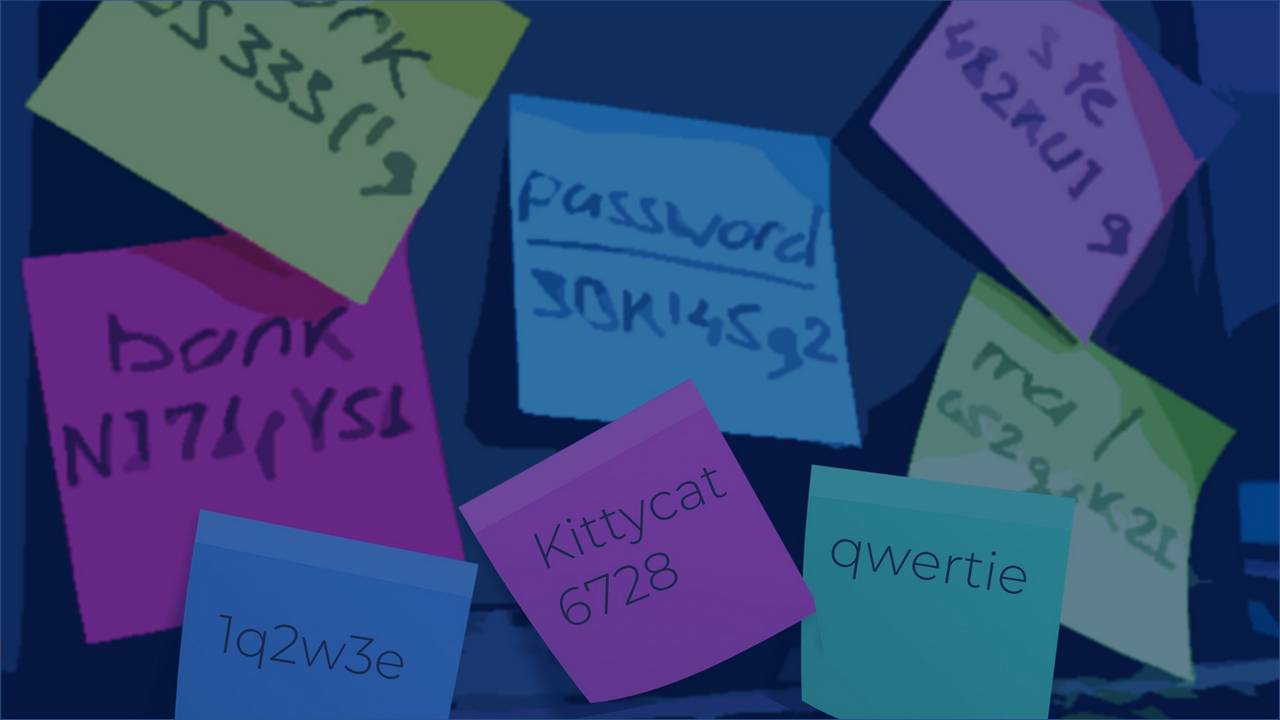
Most people cannot remember long passwords and end up storing them in a password manager, on paper, or somewhere else unsecured. The problem with an incredibly long password is that it’s something you have [stored/saved/written], not something you know/are/do. This, essentially “collapses” the attempted dual-factor down to multiple instances of a single-factor (multiple things we have). And this is exactly why the industry is moving towards passwordless authentication. Not only are passwordless options more convenient for users, but they are also more secure since multiple factors are in play. Many vendors now offer “AI”-type login authentication, which are more convenient for users and go beyond the traditional MFA approaches. For example, if a login looks suspicious (from an unknown device, or recent login from a distant location), the user will be prompted to authenticate with an added method.
My point is that it’s critical to be forward-thinking and innovative in reasoning through policies before implementing. Passwordless authentication, as with most unfamiliar things, takes us outside of our comfort zone. But with familiarity, your systems will be more secure, and your users may even thank you for saving time and making their lives easier!